If you recently came across 001-gdl1ghbstssxzv3os4rfaa-3687053746 you’re probably wondering what exactly it is. At first glance it looks random, technical and maybe even suspicious. Long strings of letters and numbers often raise questions especially when they appear in downloaded system logs or unfamiliar files.
The good news is that in most situations this type of string is not dangerous. It is typically a system generated identifier used by software to organize and track information behind the scenes.
Once you understand how modern digital systems work the mystery around it becomes much clearer. Let’s look at what this identifier really represents and when, if ever you should be concerned. Explain in Everytalkin.
What Is 001-gdl1ghbstssxzv3os4rfaa-3687053746?

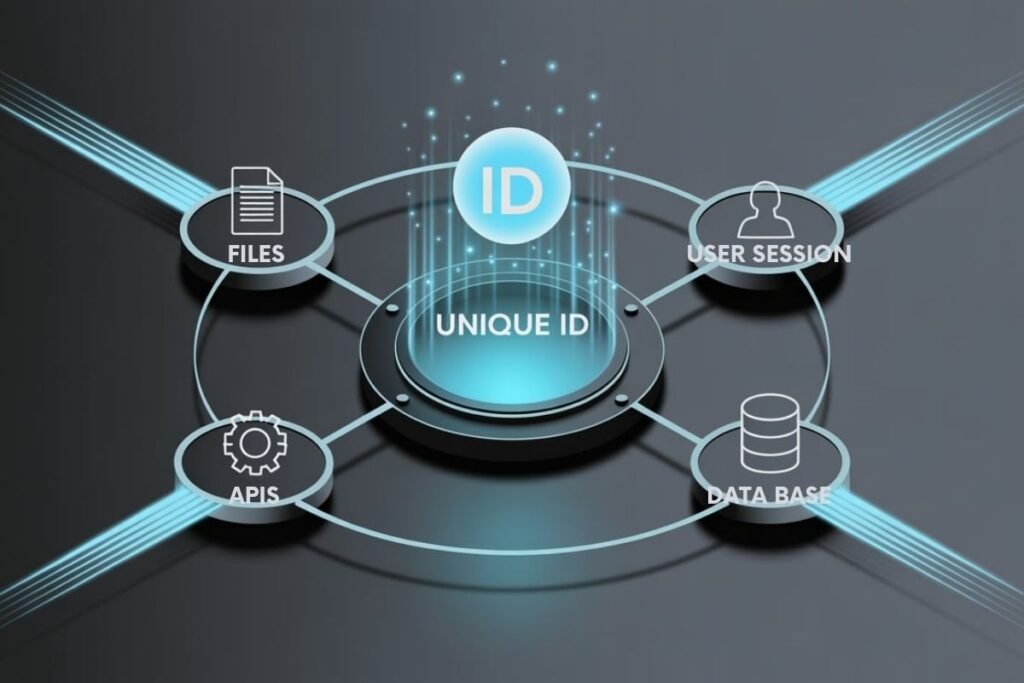
This string is best understood as a unique identifier. Software systems rely on identifiers like this to label files, database entries, sessions or transactions so they can be retrieved accurately later.
Computers do not depend on simple names such as “file1” or “recordA.” In large systems handling millions of entries names must be unique and conflict free. That is why identifiers are often long and complex. They are generated automatically using structured methods that prevent duplication.
The prefix may represent a category or internal grouping. The middle portion is usually a randomized or hashed string to ensure uniqueness. The numeric suffix can function as a reference number or internal counter. The exact meaning depends entirely on the system that created it. To a person it looks random. To a machine it is precise and meaningful.
Why Do People Search for This Code?
Most users search for identifiers like this because they appear unexpectedly. You might see it in a file name inside a URL in a system log or attached to a download. When something unfamiliar shows up it naturally triggers caution.
Common concerns include whether the string is malware, a tracking mechanism or a sign that a system has been compromised. In reality identifiers alone do nothing by themselves. They only act as references within a larger system.
Understanding that distinction removes much of the fear surrounding them.
Where Identifiers Like This Commonly Appear?
Identifiers of this format are used across many normal digital environments. Operating systems generate unique references for logs and background processes. Cloud storage systems assign IDs to files so they can be retrieved accurately.
Web applications use identifiers in URLs to fetch specific records or manage sessions. Ecommerce platforms use similar codes to track orders and inventory. Because modern infrastructure is built on structured data identifiers are everywhere even if most users never notice them.
Why Unique Identifiers Matter in Digital Systems

These identifiers form the hidden architecture of system efficiency. Without them, data would be chaotic and easily lost or misinterpreted. Here is how they support various digital functions:
Ensuring Data Traceability
Every action in a system whether it is a user logging in, a transaction occurring or a file being updated is typically associated with a unique ID. This allows system logs to show exactly what happened, when and to what.
Improving System Communication
Different parts of an app or digital infrastructure often called microservices use these identifiers to send, retrieve and synchronize data. Because the ID is unique, it eliminates the possibility of confusion or mismatch between services.
Powering Inventory and Product Management
In retail and ecommerce, every item must be identifiable in real time. These identifiers act as SKU codes, helping warehouse systems, online stores and delivery systems communicate flawlessly about stock levels, pricing and orders.
Supporting Security and Access Control
When you log into a website or application, the system uses identifiers like session tokens or user IDs to verify your identity and track your activity. This enables everything from secure login to personalized settings.
Organizing Digital Assets
In environments like digital marketing platforms or cloud services, identifiers let teams manage thousands of files or resources without redundancy or confusion.
They serve as file IDs, asset references or media locators that point to the correct version of an image, video, document or dataset.
Exploring the Components of 001-gdl1ghbstssxzv3os4rfaa-3687053746
Let’s take a deeper look at what elements typically come together in a UID like this 001-gdl1ghbstssxzv3os4rfaa-3687053746.
The prefix 001 might indicate a system or business unit. The middle portion gdl1ghbstssxzv3os4rfaa is likely a generated string using a hashing algorithm or base encoding. The suffix 3687053746 may represent a timestamp or numerical reference. Each part has meaning depending on the system’s design.
Such IDs serve a range of roles, including:
- Tracking Codes for monitoring behavior or product movement.
- Metadata Identifiers to provide information about the type, format or owner of a file.
- Content IDs used in media delivery networks to identify articles, images or videos.
- Database Keys, acting as primary or foreign keys in relational tables.
- Object References in programming to point to data instances.
- App Identifiers that map software applications to usage or updates.
When Should You Pay Attention?
Although identifiers themselves are harmless context matters. If the string is attached to an unknown executable actively running on your system repeatedly regenerates after deletion or appears alongside other suspicious activity further investigation may be wise.
In contrast if it is simply a file reference log entry or URL parameter with no unusual behavior attached there is typically nothing to worry about. A basic antivirus scan can always provide additional reassurance.
How Systems Generate Identifiers Like This?
Modern software prioritizes efficiency and scalability. Instead of checking manually whether a name is already in use, systems generate statistically unique identifiers through hashing algorithms, randomized sequences or timestamp based generators.
This approach allows millions of records to exist without duplication. It also reduces errors in distributed systems where multiple processes operate simultaneously.
The complexity of the identifier increases reliability. What seems unreadable to humans is optimized for machines.
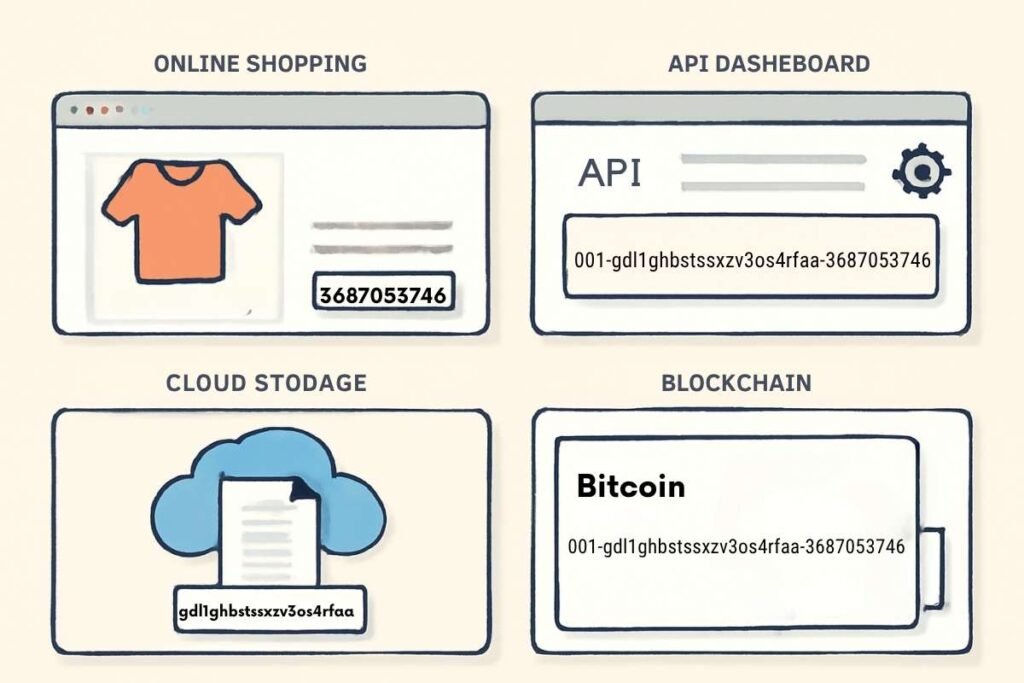
Real Life Applications of 001-gdl1ghbstssxzv3os4rfaa-3687053746
The usefulness of unique identifiers becomes clearer when you look at how they are applied across different domains.
In ecommerce platforms, the identifier could be linked to a product listing. This listing would reference a product description, price, inventory level and images all tied together under one UID. When an order is placed, this same ID helps track the transaction from warehouse to doorstep.
In software development, such identifiers often serve as session tokens or authentication tokens. They make it possible to maintain continuity in user sessions, secure API interactions and manage access levels without storing sensitive information directly.
In content management systems, an identifier ensures that digital assets like documents or videos can be edited, tracked and shared without confusion. Even if a file is renamed or moved, the identifier keeps its identity intact.
In blockchain and cloud environments, identifiers like 001-gdl1ghbstssxzv3os4rfaa-3687053746 enable users to retrieve encrypted data blocks or pinpoint transaction histories efficiently. These UIDs work seamlessly with decentralized architectures to provide consistency and security.
Conclusion
Identifiers like 001-gdl1ghbstssxzv3os4rfaa-3687053746 might seem obscure at first glance, but they are essential to the smooth operation of modern digital systems. They ensure accuracy, maintain structure and enhance communication between services and users.
Whether you are handling data, designing APIs, securing apps or managing digital products, learning to understand and use these identifiers wisely offers you greater control, organization and confidence.
As businesses continue to scale digitally, mastering identifiers will become more than just a technical skill, it will be a strategic advantage.
FAQs
What does 001-gdl1ghbstssxzv3os4rfaa-3687053746 represent?
It is a unique identifier representing a resource, transaction, file or asset in a digital system, used for precise tracking and referencing.
Are unique identifiers the same as tracking codes?
Not exactly. Unique identifiers are the core references to data or resources, while tracking codes are often temporary or specific to analytics and movement monitoring.
Can I generate my own identifiers like 001-gdl1ghbstssxzv3os4rfaa-3687053746?
Yes, using techniques like UUID generation, hashing functions or system based numbering formats, you can create custom identifiers.
Where are identifiers like 001-gdl1ghbstssxzv3os4rfaa-3687053746 stored?
Typically, they are saved in structured databases or cloud systems, often linked to metadata and protected through access control protocols.
How secure are these identifiers?
Identifiers like 001-gdl1ghbstssxzv3os4rfaa-3687053746 are generally secure, but for added protection, they should be paired with encryption, secure access methods and activity monitoring.
How do identifiers like 001-gdl1ghbstssxzv3os4rfaa-3687053746 work in APIs?
They are passed within requests either in the URL, headers or request body to access or update specific resources efficiently and accurately.